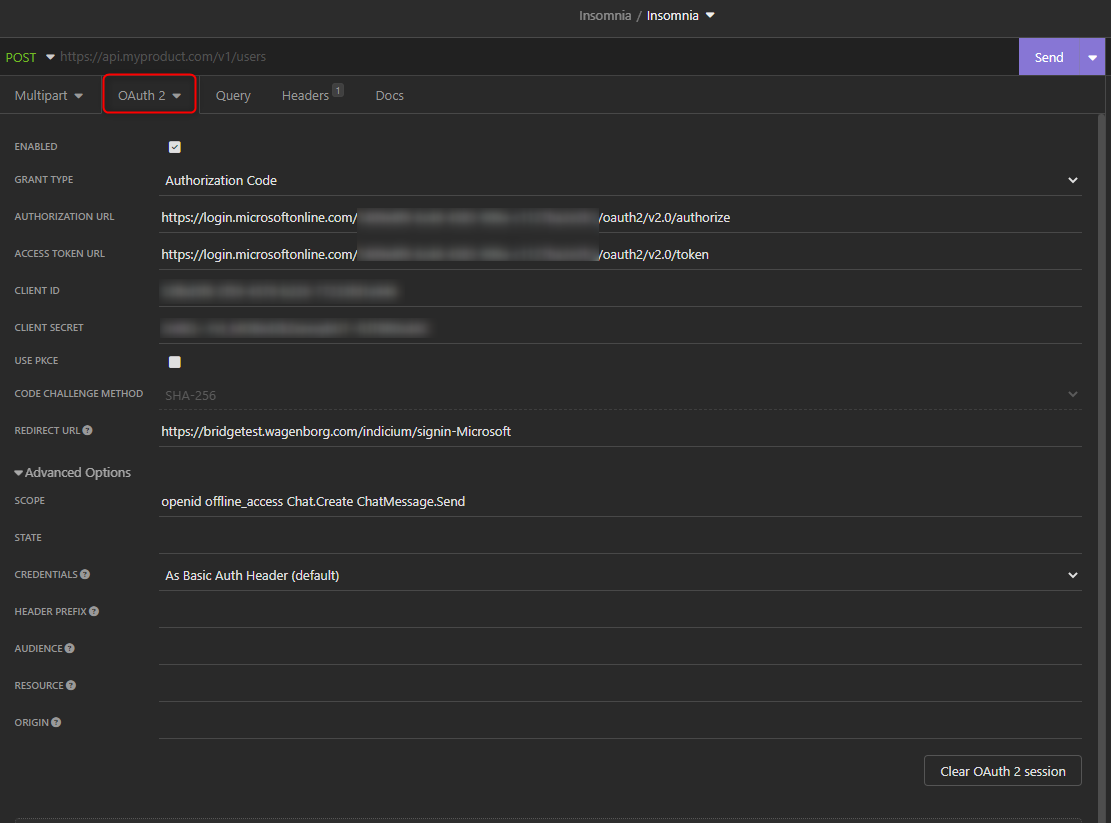
Hi. I have been fiddling around with getting a token for the Microsoft Graph API.
I want to read an email box from a fixed user and use it in an application. So I went to the AD portal, registered the App et cetera.
- When I use the v2 oauth URI's then I get an error :
-
"invalid_request AADSTS90014: The required field 'scope' is missing from the credential. Ensure that you have all the necessary parameters for the login request. - When I use the v1 oath URI's then I get a token, but whenever I try to request a resource I always get the message:
-
"message": "Access token validation failure. Invalid audience."
I really don't understand what is the solution.
How should I set this up?