Hi Tejo,
I completely agree. However, we cannot safely offer the requested functionality in a 2-tier architecture.
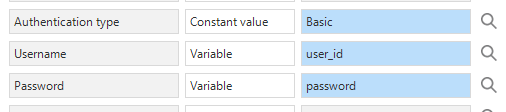
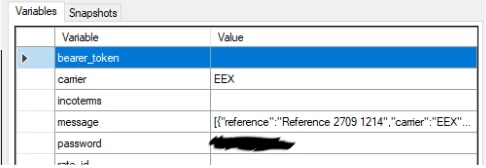
Storing passwords encrypted is certainly recommended. Data encryption is a feature already offered by the platform. This feature is not available to the 2-tier Windows GUI. Only Indicium as agent can encrypt and decrypt safely for use in (e.g.) API calls without the client ever accessing these raw data values.
We cannot offer the option to decrypt to the Windows GUI, as this would mean that the decryption keys would be available to the end user. Because of this, the feature to decrypt is exclusive to an architecture with Indicium (a system flow, Universal GUI and eventually Windows GUI on Indicium).
Hashing of passwords and checking hashed passwords is also available in the platform, also to the 2-tier Windows GUI. However, a hashed password can only be used to verify a password. The hash cannot be ‘un-hashed’ to the raw password for use in an API call.