Hi all,
I have currently in our live production System 3 separate applications for which:
- The 2 Applications share the same DB but separate GUI and subdomain access
- Universal GUI+Indicium on App Service A
- Web GUI on App Service B
- The 3rd Application separate DB and subdomain access
- Universal GUI+Indicium on App Service C
The reason we have separate App Service was to enable O365 login on App Service C, as the users of App Service A, B cannot be enabled yet. The subdomain is for creating individual uniqueness of the published app to differenciate to users.
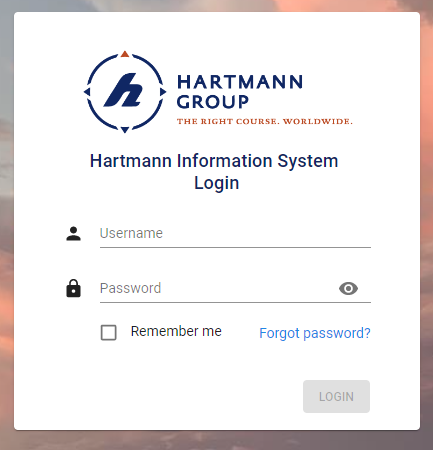
App Service A Universal GUI login:
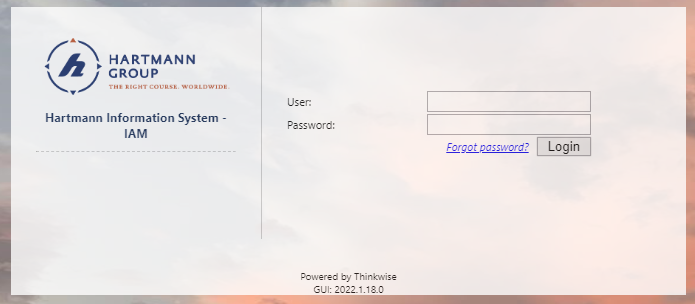
App Service B Web GUI login:
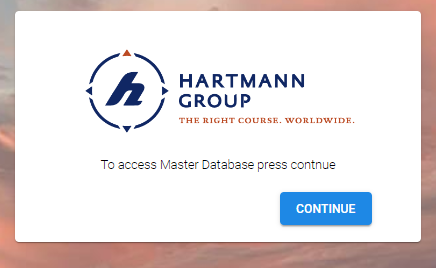
App service C Universal GUI Login with O365 only:
NOW with the 2022.2 version and the new openID Provider being configured in the IAM, there is no possibility to have the App Service A login but Only App Service C.
Questions:
- How or what can I configure to have the same specific logins as it was before?
- Is this a matter of IAM and openID Provider cannot be assigned to specific Published APP in IAM?
Comments on the OpenID provider:
If in the future I have separate O365 with ‘Microsoft’ name and ID, I cannot use a second one as the name is already taken and the App registration breaks if I use ‘Microsoft 1’ as the return urls are towards specific subdomain and only ‘Microsoft’.





