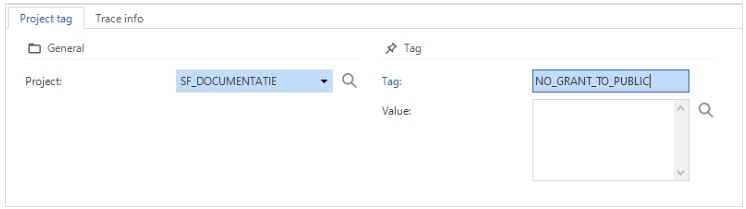
When a new release is created, the SQL scripts contains statement like
‘grant … on … to public’
The role public is part of every user who can make connection with the database. This results in the effect that I’m not able to give developers rights to look into production databases, because if I give these rights, they are also able to mutate the content of the database.
In my configuration only the applicationpooluser of indicium/indicium universal/webgui needs rights to the database.
So, my request is not to grant rights to the role public, but to a rolename defined by myself. This gives me the ability to create a difference between the rights of the applicationpooluser and any other users I want to give access to the database.