Many organizations elect to audit access to provide insight into application usage and potential security issues. In the Intelligent Application Manager (IAM) version 2020.2 a logging mechanism is introduced which makes these audits possible.
Auditing
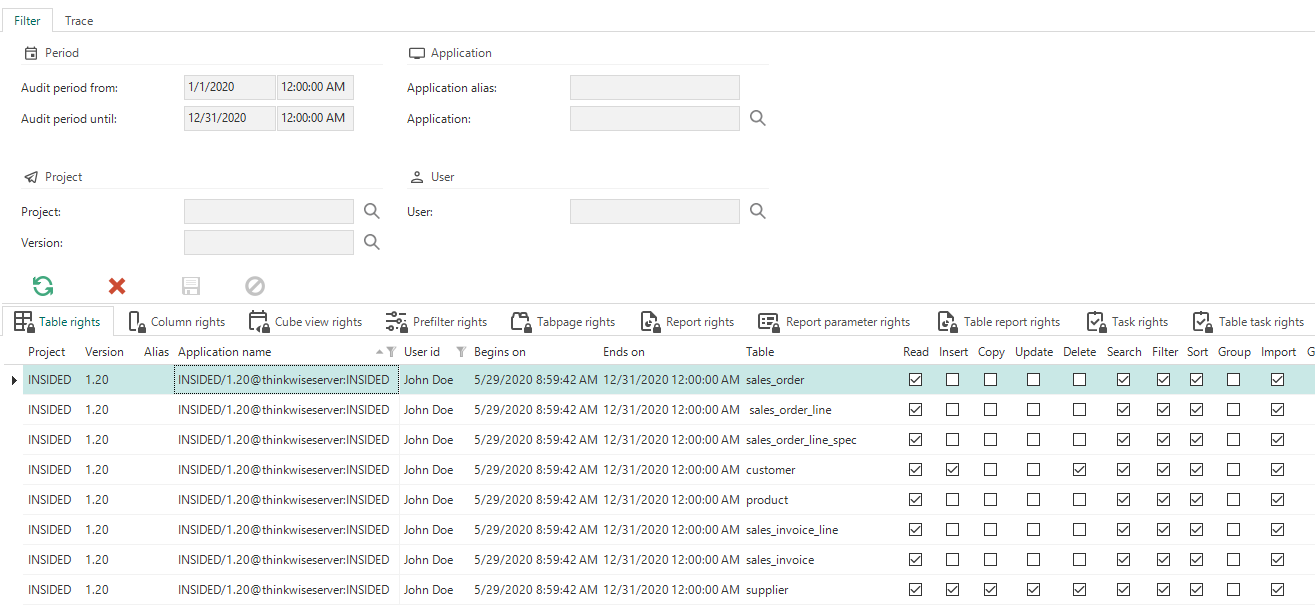
The purpose of auditing is to be able to see which user had access to a certain object in one of the applications at a certain time. To access this information, an Auditing group is present in the Advanced menu, which includes an Access Analysis menu item. The corresponding screen looks like this:
Access analysis
A filter is included at the top of the screen. In this filter you can enter a Audit period from and a Audit period to in the Period section. IAM will then calculate what the maximum access rights of a user are for a specific object in a specific application during that period.
The results of this calculation can be found in the tabs in the bottom half of the screen. A tab is available for each object that can be authorized. The results of the calculation can contain a lot of data. Filtering on more properties, besides Audit period from and Audit period to, will reduce the set of data. If Project and Project version are filled, IAM will filter the data on all applications based on it. You can filter even more specifically under applications. Application alias provides data of a specific application, regardless of the version. When the Application itself is filled, filtering is also done on the version of the application and on the server where the application is located. Finally, you can filter on User. If this field is filled, IAM will only display access data from that specific user.
Logging
The purpose of logging in IAM is to be able to determine when a record was changed and what that change was. IAM maintains logs for Roles, OpenID and general data about projects and users. The logs can be found via the Advanced menu, menu group Logging and then History Analysis.
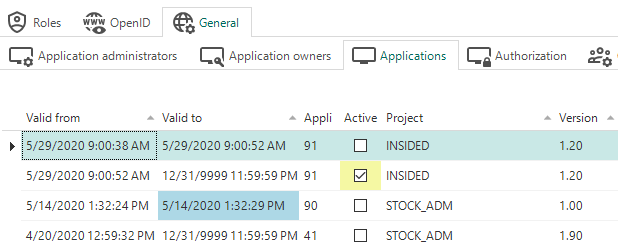
The example below shows the Applications tab on the History Analysis screen. The list of data includes all changes made to all records in Applications. If a cell is colored yellow, the value of the column that contains the cell has changed. If the Valid to field is blue, the record has been deleted. The moment of the deletion is stored in the Valid to field.
Application history
Usage of Auditing in combination with Logging
It is best practice to use Auditing in combination with Logging. Authorization analysis starts in Auditing. Here, certain data can raise questions and then the logs can be used to see how a certain situation has arisen. For example: a user had access to table A in January 2020. The logging can then be searched by taking the following steps:
-
Search in which groups the user was a member during that period;
-
Search to which roles those groups were linked during that period;
-
Search in which of those roles the table did have read rights.


